

February 16, 2026
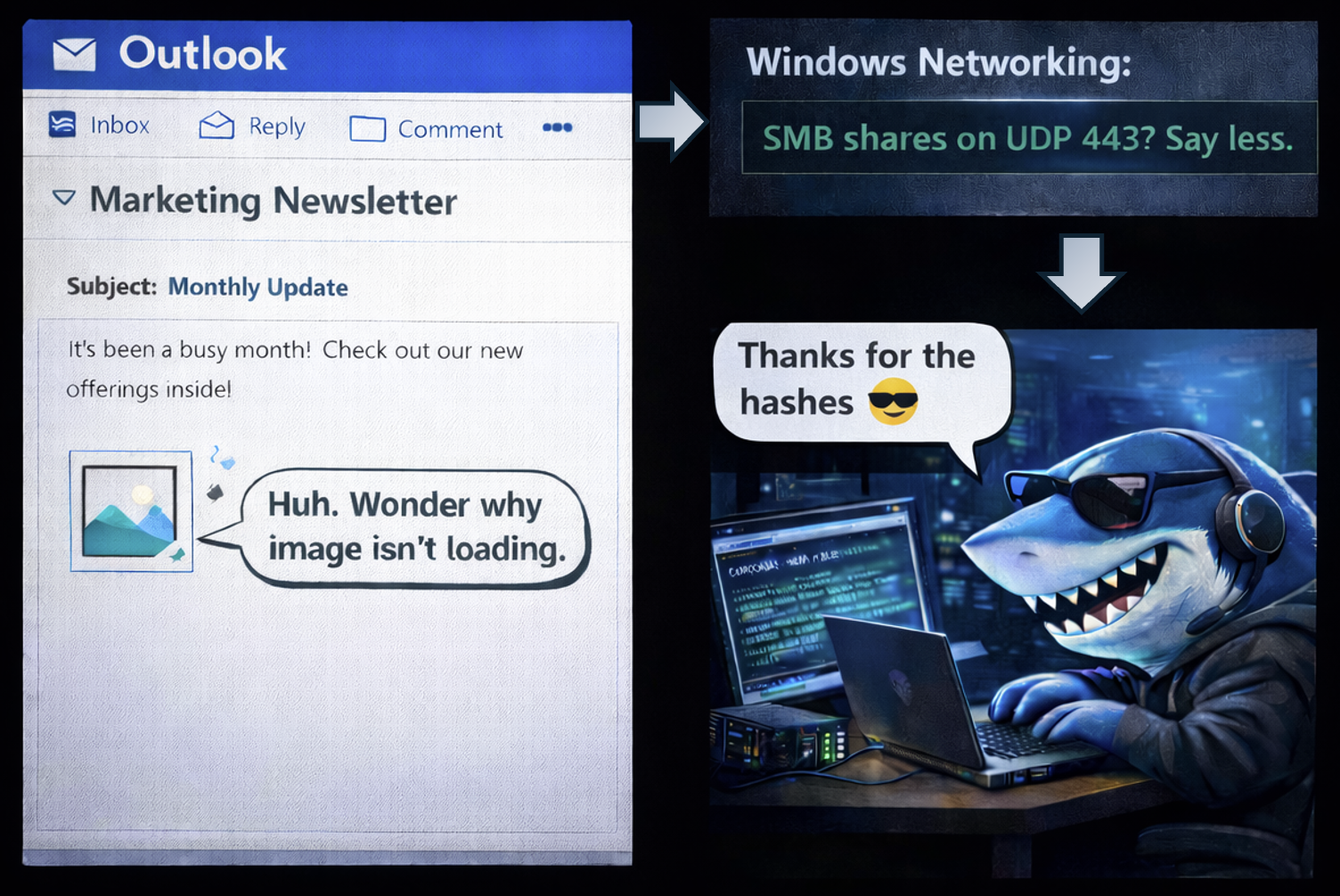
Abusing forced authentication for credentialed access and privilege escalation.
February 1, 2026
Common backup related weaknesses and how they can be exploited by an attacker.

October 8, 2025
An overview of physical security weaknesses and common bypass techniques.
July 1, 2025
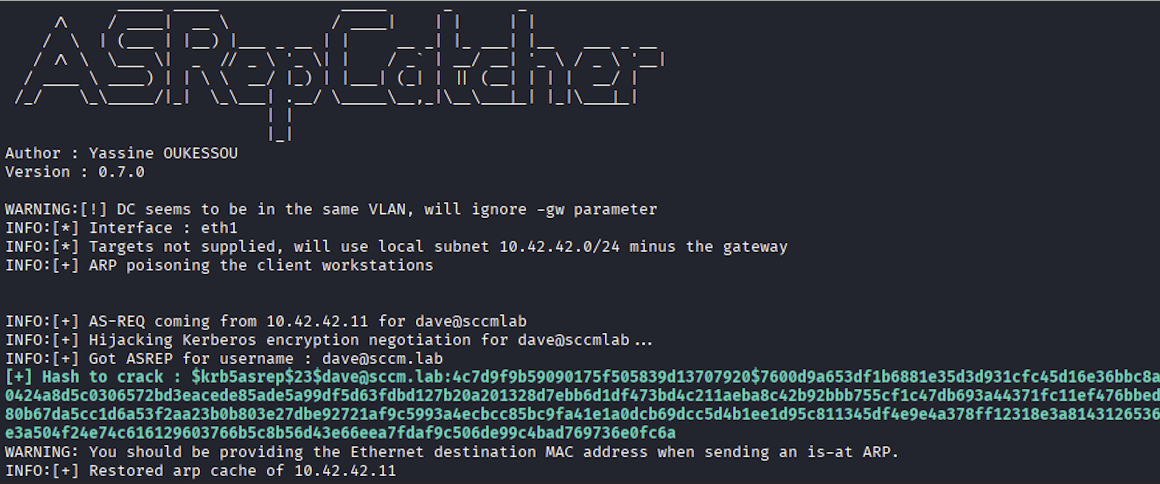
ARP poisoning techniques that enable interception of Kerberos authentication traffic to steal domain credentials.